How to Connect
iOS Client
- Download the WireGuard app from the App Store
- Open the WireGuard app
- Tap the "+" button and select "Create from QR code"
- Scan the QR code below
- Give the VPN a name (optional)
- Tap "Add Tunnel"
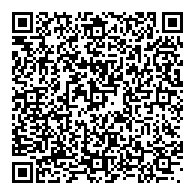
iOS Client Configuration
Android Client
- Download the WireGuard app from Google Play
- Open the WireGuard app
- Tap the "+" button
- Select "Scan from QR code"
- Scan the QR code below
- Give the VPN a name (optional)
- Tap "Create Tunnel"
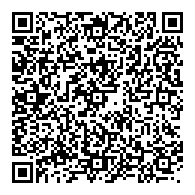
Android Client Configuration